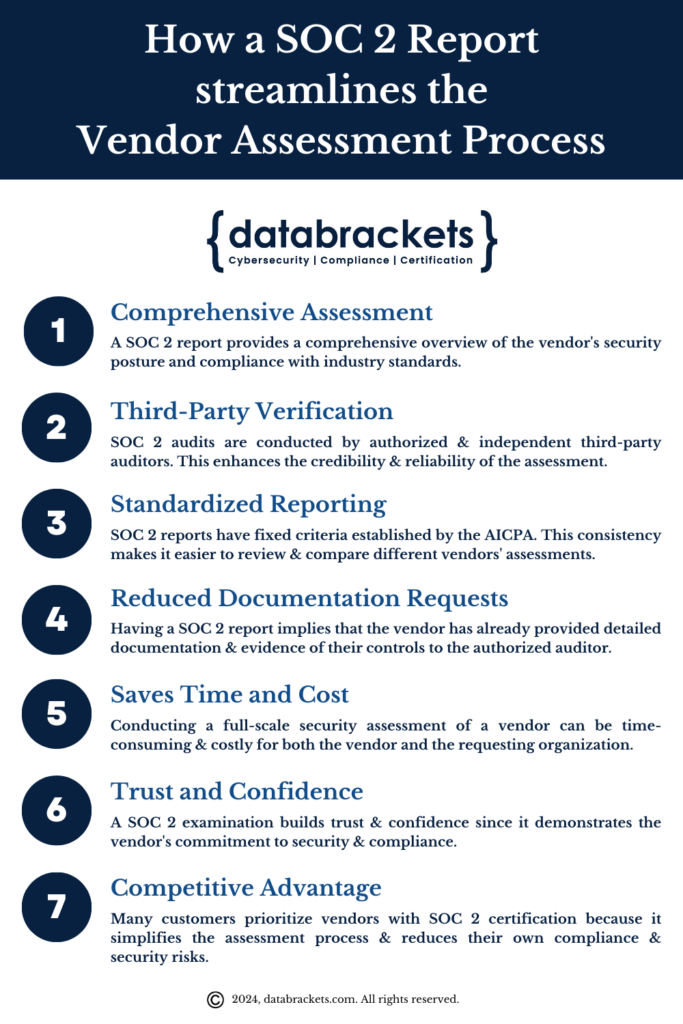
When you hand your data to a third-party vendor, you’re placing enormous trust in their security practices. But how do you know that trust is well-placed? That’s exactly where SOC 2 certification verification comes in. If a vendor claims to be SOC 2 compliant, you have every right — and responsibility — to confirm it.
This article walks you through how to verify SOC 2 certification in plain language. Whether you’re a procurement officer, a startup founder, or an IT manager evaluating a SaaS tool, you’ll walk away knowing precisely what to ask, what to review, and what red flags to watch for.
What Is SOC 2 Certification and Why Does It Matter?
Before learning how to verify SOC 2 certification, it helps to understand what it actually is. SOC 2 stands for System and Organization Controls 2. It is a voluntary auditing standard developed by the American Institute of Certified Public Accountants (AICPA) that evaluates how a service organization handles customer data.
SOC 2 is built around five Trust Services Criteria (TSC):
| Trust Service Criteria | What It Covers |
|---|---|
| Security | Protection against unauthorized access (required for all audits) |
| Availability | System uptime and performance commitments |
| Processing Integrity | Completeness and accuracy of data processing |
| Confidentiality | Protection of confidential business information |
| Privacy | Handling of personal information per privacy standards |
“SOC 2 reports are intended to meet the needs of a broad range of users that need detailed information and assurance about the controls at a service organization relevant to security, availability, and processing integrity of the systems the service organization uses.” — AICPA
Suggested read: LMS Certification Programs: Everything You Need to Know Before You Enroll
Unlike ISO 27001, which is a certification with a pass/fail outcome, SOC 2 is an audit report. This is a critical distinction. There is no central registry where you can simply look up “certified” vendors. Verification requires reviewing an actual audit report issued by a qualified CPA firm.
SOC 2 Type I vs. Type II: What’s the Difference?
When you verify SOC 2 certification, one of the first things you’ll encounter is the distinction between Type I and Type II reports.
SOC 2 Type I
- Evaluates whether controls were designed appropriately at a single point in time
- Faster and less expensive for vendors to obtain
- Less rigorous — it only confirms controls exist, not that they work over time
SOC 2 Type II
- Evaluates whether controls operated effectively over a period of time (typically 6–12 months)
- Considered the gold standard for vendor due diligence
- Demonstrates sustained commitment to security, not just a snapshot
Key takeaway: Always prefer vendors with a SOC 2 Type II report. A Type I report alone is a starting point — not a seal of ongoing security excellence.
How to Verify SOC 2 Certification: A Step-by-Step Process
Step 1: Request the Actual SOC 2 Report
The most direct way to verify a vendor’s SOC 2 status is to ask for a copy of the full audit report. A reputable vendor will make this available under an NDA (Non-Disclosure Agreement) because the report contains sensitive details about their internal controls.
What to request:
- The full SOC 2 Type II report (not just a summary or badge)
- The auditor’s opinion letter (included within the report)
- The period covered by the audit
⚠️ Red flag: If a vendor refuses to share any portion of their SOC 2 report, or only shares a marketing one-pager that says “SOC 2 Compliant,” that is a warning sign. Legitimate vendors are accustomed to sharing reports under NDA.
Suggested read: Peptide Certification: Everything You Need to Know Before You Start
Step 2: Verify the Auditor Is a Licensed CPA Firm
SOC 2 audits can only be conducted by licensed Certified Public Accountant (CPA) firms registered with the AICPA. This is non-negotiable. If the report was not issued by a CPA firm, it is not a valid SOC 2 report.
How to verify the auditor:
- Look up the CPA firm on the AICPA’s directory at aicpa-cima.com
- Confirm the firm is a licensed public accounting firm in their state
- Check that the firm specializes in SOC audits (look for their experience in IT/technology audits)
Some of the most respected SOC 2 auditing firms include:
- Deloitte
- EY (Ernst & Young)
- PwC (PricewaterhouseCoopers)
- KPMG
- Smaller specialized firms like Schellman & Company, A-LIGN, and Coalfire
Step 3: Check the Audit Period and Report Date
A SOC 2 report is not a permanent credential. It covers a specific time period — often 12 months — and becomes stale after that window passes.
What to look for:
- Report issuance date: When was the audit completed?
- Audit period: What 12-month (or 6-month) window does the report cover?
- Gap analysis: Is there a significant gap between the audit period end date and today?
Industry best practice: If a SOC 2 Type II report is more than 12 months old, request an updated report or a bridge letter confirming no material changes have occurred since the last audit.
Suggested read: Dream Catchers Hair Extension Certification: Everything You Need to Know Before You Enroll
A vendor that hasn’t renewed their SOC 2 audit in over a year may have allowed controls to lapse or changed their infrastructure significantly. Recency matters.
Step 4: Read the Auditor’s Opinion
Inside every SOC 2 report is an auditor’s opinion letter. This is the most important section to read when you want to know how to verify SOC 2 certification properly.
There are four types of auditor opinions:
| Opinion Type | What It Means |
|---|---|
| Unqualified (Clean) | Controls were suitably designed and operated effectively — the best outcome |
| Qualified | Controls were generally effective, but there were specific exceptions or limitations |
| Adverse | Controls were not effective — a serious red flag |
| Disclaimer of Opinion | Auditor could not obtain sufficient evidence to form an opinion |
What you want to see: An unqualified opinion for all Trust Services Criteria relevant to your use case.
If the report contains a qualified or adverse opinion, ask the vendor to explain each exception in writing, and evaluate whether those exceptions affect your specific use case.
Step 5: Review the System Description
The SOC 2 report includes a detailed System Description written by the vendor. This section describes the scope of the audit — what systems, data centers, personnel, and processes were included.
Suggested read: Is Advanced Medical Certification Legit? What You Need to Know Before Enrolling
Ask yourself:
- Does the system description cover the specific product or service you’re purchasing?
- Does it include the data centers or cloud regions where your data will be stored?
- Are the subservice organizations (e.g., AWS, Azure) identified and addressed?
It’s entirely possible for a vendor to obtain SOC 2 on a narrow subset of their platform while leaving other parts unaudited. Always confirm that the system description matches your actual deployment.
Step 6: Examine the Control Exceptions
The detailed testing section of a SOC 2 report lists every control tested, the auditor’s test procedure, and any exceptions found. An exception means a control did not perform as intended during the audit period.
Not all exceptions are equal. A minor exception in a low-risk area is very different from an exception in access management or encryption. When reviewing exceptions:
- Count the number of exceptions
- Assess the severity and frequency
- Ask the vendor what remediation steps were taken
- Request a management response or remediation plan
A few minor exceptions in an otherwise clean report are common. Numerous or high-severity exceptions should raise concerns.
Step 7: Verify Using Third-Party Tools and Trust Centers
Many modern SaaS vendors now publish their compliance status on trust center platforms. These platforms can serve as a quick-start verification layer before diving into the full report.
Suggested read: How to Earn Your Online Principal Certification Programs in Texas: Everything Aspiring School Leaders Need to Know
Popular trust center and compliance platforms:
- Vanta — Many vendors publish live compliance dashboards
- Drata — Real-time SOC 2 monitoring with audit evidence
- Tugboat Logic — Vendor compliance summaries
- SecurityScorecard — External security ratings
Important: Trust center dashboards are helpful for a first look, but they do not replace a review of the actual audit report. Use them as a starting point, not an endpoint.
Common Mistakes When Verifying SOC 2 Certification
Even experienced procurement teams make errors. Here are the most common mistakes to avoid:
- Accepting a SOC 2 badge or logo as proof — These are marketing assets, not verified credentials.
- Not checking the audit period — An old report may no longer reflect current controls.
- Ignoring subservice organizations — Cloud hosting providers, payment processors, or other subcontractors may be excluded from the audit scope.
- Skipping the exceptions section — A report with dozens of exceptions is very different from one with none.
- Confusing SOC 1 with SOC 2 — SOC 1 focuses on financial reporting controls; SOC 2 focuses on security and data handling.
- Not requesting the Type II report — Only accepting a Type I report misses the ongoing effectiveness testing.
What Does a Legitimate SOC 2 Report Contain?
When you receive a SOC 2 report and want to know how to verify SOC 2 certification documents are authentic, look for these sections:
| Report Section | Description |
|---|---|
| Independent Service Auditor’s Report | The CPA firm’s official opinion letter |
| Management’s Assertion | Statement from the vendor about their controls |
| System Description | Detailed description of the in-scope systems |
| Trust Services Criteria | The specific criteria evaluated (Security, Availability, etc.) |
| Tests of Controls and Results | Each control tested, method used, and any exceptions noted |
A full SOC 2 Type II report is typically 50 to 200+ pages long. If someone hands you a 5-page document and calls it a SOC 2 report, it is almost certainly incomplete.
Suggested read: Gift Certificate Tracking Software: Everything You Need to Know Before You Buy
Case Study: How a Mid-Size Fintech Company Verified SOC 2 Before Signing a $2M SaaS Contract
A financial technology company was evaluating a cloud-based data analytics vendor before signing a multi-year enterprise agreement. The vendor prominently displayed a “SOC 2 Certified” badge on their website.
What the procurement team did right:
- Requested the full SOC 2 Type II report under NDA
- Verified the auditing CPA firm’s license through the AICPA directory
- Noted that the audit period ended 14 months prior — already outside the 12-month best practice window
- Discovered 3 exceptions in the access management controls section
- Asked the vendor for their management response and remediation plan
Outcome: The vendor provided documentation showing all three exceptions had been remediated and offered a bridge letter from the auditor confirming no material changes. The contract was signed — but with a contractual requirement for the vendor to provide an updated SOC 2 Type II report within 90 days.
Lesson: Even reputable vendors may have gaps. Verification isn’t about distrust — it’s about informed partnership.
How to Verify SOC 2 Certification for Cloud Providers Specifically
When your vendor uses a major cloud provider like AWS, Azure, or Google Cloud, the shared responsibility model adds complexity.
Key things to check:
Suggested read: Sclerotherapy Certification: What You Need to Know Before You Start Treating Veins
- Does the vendor’s SOC 2 report reference their cloud provider as a subservice organization?
- Does the report use the carve-out method (excludes the cloud provider’s controls) or the inclusive method (includes them)?
- If using the carve-out method, has the vendor provided complementary user entity controls to fill the gap?
AWS, Azure, and Google Cloud all publish their own SOC 2 Type II reports. Your vendor’s SOC 2 report should complement these, not duplicate them.
SOC 2 Verification Checklist
Use this checklist every time you evaluate a vendor’s SOC 2 compliance:
- [ ] Received full SOC 2 Type II report (not just Type I)
- [ ] Confirmed audit was conducted by a licensed CPA firm
- [ ] Verified auditor’s license via AICPA directory
- [ ] Confirmed audit period is within the last 12 months
- [ ] Obtained bridge letter if report is 12+ months old
- [ ] Read auditor’s opinion — confirmed unqualified opinion
- [ ] Reviewed system description — confirmed it covers your use case
- [ ] Checked for exceptions and reviewed vendor’s remediation plan
- [ ] Identified subservice organizations and their treatment
- [ ] Noted which Trust Services Criteria were covered
How Often Should You Re-Verify SOC 2 Certification?
Verifying SOC 2 once is not enough. Vendor security postures change. Personnel change. Infrastructure changes. Best practices for ongoing verification:
- Annually: Request an updated SOC 2 Type II report from every critical vendor
- After significant changes: If a vendor undergoes a merger, acquisition, major platform migration, or data breach, request a new report immediately
- At contract renewal: Make updated SOC 2 reports a contractual requirement at each renewal
- Continuously: Monitor vendor trust centers or use a third-party risk management (TPRM) platform that tracks vendor compliance in near-real time
Internal Link: Managing Vendor Credentials and Digital Assets
If your organization handles digital products or client-facing assets, knowing how to manage and verify credentials is part of a broader operational discipline. For example, if you sell digital products or services through your website, you may want to explore tools like gift certificate Squarespace integrations to manage client-facing transactions securely — especially as you’re building trust with customers who want assurance that their purchases and data are protected.
Why SOC 2 Verification Protects Your Business
The stakes of skipping SOC 2 verification are real:
- Data breaches: An unvetted vendor with weak access controls can expose your customer data.
- Regulatory liability: If you’re subject to HIPAA, GDPR, or CCPA, a vendor breach can trigger compliance violations for your organization.
- Reputational damage: Customers hold businesses accountable for their vendor choices.
- Financial loss: The average cost of a data breach in 2024 was $4.88 million, according to IBM’s Cost of a Data Breach Report.
“Organizations are only as secure as their weakest vendor.” — A widely cited principle in third-party risk management
Suggested read: Online Marriage and Family Therapy Certificate Programs: Everything You Need to Know Before You Enroll
SOC 2 verification is not paperwork for its own sake. It is a meaningful, practical due diligence step that reduces your exposure.
Frequently Asked Questions About How to Verify SOC 2 Certification
What is the fastest way to verify SOC 2 certification?
The fastest initial check is to visit the vendor’s trust center or ask their sales team for a SOC 2 summary. However, genuine verification requires reviewing the full audit report — including the auditor’s opinion, audit period, system description, and exceptions.
Is there a public registry of SOC 2 certified companies?
No. Unlike some certifications, there is no centralized public SOC 2 registry. SOC 2 reports are confidential documents shared directly with customers under NDA. The AICPA does not maintain a searchable list of SOC 2-compliant companies.
Can I trust a SOC 2 badge on a vendor’s website?
Not on its own. A SOC 2 badge is a marketing asset, not a verified credential. It should prompt you to request the actual report, but it is not verification in itself.
What’s the difference between SOC 2 and ISO 27001?
- SOC 2 is an audit report specific to U.S. standards, focused on Trust Services Criteria, issued by a CPA firm.
- ISO 27001 is an international certification with a formal pass/fail outcome, focused on an Information Security Management System (ISMS). Both are credible, but they measure different things. Many global vendors pursue both.
How do I know if a SOC 2 report has been tampered with?
Verify the CPA firm’s identity independently and contact them if you have any concerns. You can also look for the auditor’s digital signature or firm letterhead details. When in doubt, call the CPA firm directly to confirm they issued the report.
How long does it take to verify SOC 2 certification?
A surface-level check can take 30 minutes. A thorough review of a full SOC 2 Type II report, including the exceptions section, may take several hours depending on report length and complexity. For enterprise contracts, consider involving your legal or compliance team.
Suggested read: ITDS Certification: Everything You Need to Know About Becoming an Infant Toddler Developmental Specialist
What should I do if a vendor won’t share their SOC 2 report?
First, confirm they have offered it under NDA — many vendors require you to sign an NDA before sharing. If they refuse even under NDA, treat this as a significant red flag and escalate internally before proceeding with the contract.
Call to Action: Start Verifying SOC 2 Certification Today
Don’t wait until a vendor incident to wish you had done your homework. Now that you know how to verify SOC 2 certification step by step, it’s time to apply this process to every critical vendor in your ecosystem.
Here’s what to do right now:
- List your top 10 vendors who handle sensitive data
- Request their most recent SOC 2 Type II report under NDA
- Use the checklist in this article to evaluate each report
- Document findings and build them into your vendor risk management program
Learning how to verify SOC 2 certification is one of the most impactful things your security or procurement team can do this quarter. The process is straightforward once you know what to look for — and the protection it provides is well worth the time investment.
Citations and Sources
- AICPA — SOC 2® — SOC for Service Organizations: Trust Services Criteria: https://www.aicpa-cima.com/resources/landing/system-and-organization-controls-soc-suite-of-services
- IBM Security — Cost of a Data Breach Report 2024: https://www.ibm.com/reports/data-breach
- AICPA Trust Services Criteria (2017, updated 2022): https://www.aicpa-cima.com/cpe-learning/publication/trust-services-criteria-OPL
- Vanta — What is a SOC 2 Report?: https://www.vanta.com/resources/soc-2-report
Last updated: March 2026 | Category: Cybersecurity & Vendor Due Diligence