What Is the Entrust R Certificate That Expires on Chase?
When you log in to your Chase bank account online, your browser quietly performs a sophisticated security handshake in the background. At the heart of this process is an SSL/TLS certificate — a small digital file that proves the website you are visiting is legitimate and that your connection is encrypted. One of the most talked-about certificates tied to major financial institutions, including Chase, is the Entrust R certificate, officially known as certificates issued under Entrust’s Root Certificate Authority (CA) hierarchy.
The phrase “certificate entrust r expires chase” refers to a specific concern: SSL/TLS certificates that were issued by Entrust Datacard (now simply called Entrust) to JPMorgan Chase or its affiliated digital services reaching their expiration date. These certificates carry validity periods — typically one to two years — and once they expire, browsers immediately flag the associated website as untrusted or potentially dangerous.
Entrust is one of the oldest and most respected Certificate Authorities in the world. Founded in 1999, it has been issuing digital identity certificates to governments, banks, and enterprise organizations for over two decades. Chase, being one of the largest financial institutions in the United States with over $3.9 trillion in assets (as of 2024), depends heavily on a layered infrastructure of SSL certificates to keep its millions of users safe online.
“Digital certificates are the backbone of internet trust. When one expires on a financial platform, the ripple effect on user confidence can be immediate and significant.” — Cybersecurity Industry Expert
How the Certificate Chain Works
The certificate chain that connects Chase’s websites to Entrust’s root authority typically looks like this:
| Certificate Level | Role |
|---|---|
| Root Certificate (Entrust Root CA) | The ultimate trust anchor, stored in browsers |
| Intermediate Certificate (Entrust R3 / R2) | Bridges root to end-entity certificates |
| End-Entity Certificate (Chase’s website) | Issued directly to chase.com |
Each layer of this chain must be valid, trusted, and unexpired for your browser to establish a secure connection without throwing a warning. When the Entrust R intermediate or root certificate expires, the entire chain can break — even if Chase’s own end-entity certificate is still technically valid.
Why Does the Entrust R Certificate Expire on Chase Platforms?
Every SSL/TLS certificate has a built-in expiration date, and this is by design — not by accident. The expiration mechanism is a deliberate security feature built into the Public Key Infrastructure (PKI) ecosystem. Here is why expiration exists and why it specifically matters for the Entrust R certificate on Chase.
1. Security Hygiene and Key Rotation
Cryptographic keys can potentially be compromised over time. By forcing certificates to expire, the industry ensures that even if a private key were ever stolen, the window of exploitation is limited. The CA/Browser Forum — the governing body that sets certificate standards — has progressively shortened the maximum validity period from 5 years to just 398 days (approximately 13 months) for public-facing SSL certificates. Chase, like all major institutions, must renew its certificates regularly to stay compliant.
Suggested read: Alarm Certificate: What It Is, Why You Need One, and How It Saves You Money on Insurance
2. Algorithm Deprecation
Older Entrust certificates, particularly those from legacy root hierarchies labeled “Entrust.net Certification Authority (2048)” or “Entrust Root Certification Authority – G2”, were sometimes signed using cryptographic algorithms that have since become outdated. As browsers and operating systems deprecate older algorithms (like SHA-1, for example), any certificate relying on them becomes untrusted — effectively expiring in practical terms even before its nominal expiration date.
3. Entrust’s Own Certificate Hierarchy Updates
Entrust has updated its certificate hierarchy multiple times over the years. Their root and intermediate CAs — including Entrust R2, Entrust R3, and newer variants — each carry their own validity windows. Here is a quick reference table:
| Entrust Root / Intermediate | Approximate Expiration |
|---|---|
| Entrust.net CA (2048) | December 31, 2029 |
| Entrust Root CA – G2 | December 7, 2030 |
| Entrust Root CA – G4 | May 27, 2043 |
| Entrust Intermediate CA – L1K | January 20, 2026 |
| Entrust Intermediate CA – L1M | July 20, 2027 |
When an intermediate certificate like L1K approaches expiration, every end-entity certificate (including those issued to Chase) that chains up to that intermediate becomes at risk of generating browser warnings — even if the end-entity certificate’s own expiration date is still far in the future. This is precisely the kind of scenario behind many “certificate entrust r expires chase” incidents reported by end users.
4. Operational Oversights
Despite modern certificate management tools, certificate expiration incidents still happen to even the largest organizations. A study by Venafi found that 79% of enterprises experienced at least one certificate-related outage or disruption in a given year. Financial institutions are not immune. The sheer volume of certificates that a bank like Chase must manage — spanning web applications, mobile APIs, internal systems, and third-party integrations — makes it operationally complex to ensure that no certificate slips through the cracks.
How SSL Certificate Expiration Affects Chase Customers
The practical impact of a certificate entrust r expiring on Chase can range from mildly inconvenient to genuinely alarming, depending on your browser, device, and the specific nature of the expiration. Here is a detailed breakdown of what customers actually experience.
Browser Warning Screens
The most visible consequence is the browser warning screen. When a certificate expires or becomes untrusted, Google Chrome, Mozilla Firefox, Microsoft Edge, and Apple Safari all display full-page interstitial warnings. These typically say something like:
- “Your connection is not private” (Chrome — Error: ERR_CERT_DATE_INVALID)
- “Warning: Potential Security Risk Ahead” (Firefox — Error: SEC_ERROR_EXPIRED_CERTIFICATE)
- “This site is not secure” (Edge)
- “Safari Can’t Establish a Secure Connection” (Safari)
These warnings are designed to stop users in their tracks. For most everyday users, they are deeply alarming — and for good reason. However, when the cause is simply a certificate expiry or trust chain issue rather than an actual attack, the warning can be a false alarm from the user’s perspective.
Online Banking Disruptions
If the Entrust R certificate tied to Chase’s online banking portal expires, users may be completely unable to log in. Mobile banking apps that rely on certificate pinning — a security technique where the app only accepts connections from a specific known certificate — can crash or refuse to connect entirely. This effectively locks customers out of their accounts until Chase resolves the issue.
Suggested read: Certificate of Insurance for Workers Compensation: What Every Business Owner Must Know
Business and Commercial Banking Impact
Chase is not just a consumer bank. It serves thousands of businesses through Chase Business Banking and the JPMorgan commercial banking division. Certificate disruptions on APIs used by businesses for payroll, wire transfers, and treasury management can cascade into significant financial and operational problems. A single hour of downtime for a corporate treasury API can disrupt millions of dollars in transactions.
Customer Trust Erosion
Even after the technical issue is resolved, the reputational damage can linger. Research from IBM’s Cost of a Data Breach Report shows that customer trust, once damaged, takes months or even years to fully recover. While a certificate expiry is not the same as a data breach, customers who are repeatedly confronted with security warnings — even false alarms — begin to question whether their financial institution is truly keeping them safe.
Understanding Entrust as a Certificate Authority
To fully understand the “certificate entrust r expires chase” issue, it is essential to understand who Entrust is and what role they play in the internet’s trust ecosystem.
Entrust is a Publicly Trusted Certificate Authority (CA), which means their root certificates are pre-installed in the trust stores of all major operating systems and browsers. These trust stores — maintained by Mozilla, Apple, Microsoft, and Google — are essentially whitelists of CAs that have been vetted and approved to issue trusted SSL/TLS certificates.
Key Facts About Entrust
- Founded: 1999
- Headquarters: Addison, Texas, USA
- Certificates Issued: Millions across government, banking, healthcare, and enterprise
- Key Products: SSL/TLS certificates, code signing certificates, digital identity solutions
- Compliance: Audited annually under WebTrust for CAs standards
How Entrust’s Certificate Hierarchy Works
Entrust operates a hierarchical certificate structure. At the top sits their Root CA — an offline certificate stored in an air-gapped, highly secure facility. Below it are intermediate or subordinate CAs (often labeled R1, R2, R3, L1K, L1M, etc.). These intermediates are the ones that actually sign the end-entity certificates used by organizations like Chase.
The “R” in Entrust R certificates typically refers to the Root CA hierarchy or the specific subordinate CA generation. When users search for “certificate entrust r expires chase,” they are often referencing these intermediate-level certificates, which have shorter validity periods than root certificates and therefore expire more frequently.
What Happens When the Entrust R Certificate Expires on Chase?
The technical sequence of events following a certificate expiry is worth understanding in detail, because it helps explain why these incidents can sometimes affect millions of users simultaneously — and why they can be so difficult to resolve quickly.
Step-by-Step: The Expiry Cascade
Step 1: Certificate Validity Check
When your browser connects to chase.com, it downloads the certificate chain presented by Chase’s servers. It checks each certificate’s “Not After” field — the expiration date encoded directly into the certificate.
Suggested read: What Is a Workers Comp Insurance Certificate and Why Does Your Business Actually Need One?
Step 2: Chain Validation
Your browser verifies that each certificate in the chain is signed by the one above it, all the way up to a trusted root. If the Entrust R intermediate has expired, this chain validation fails immediately.
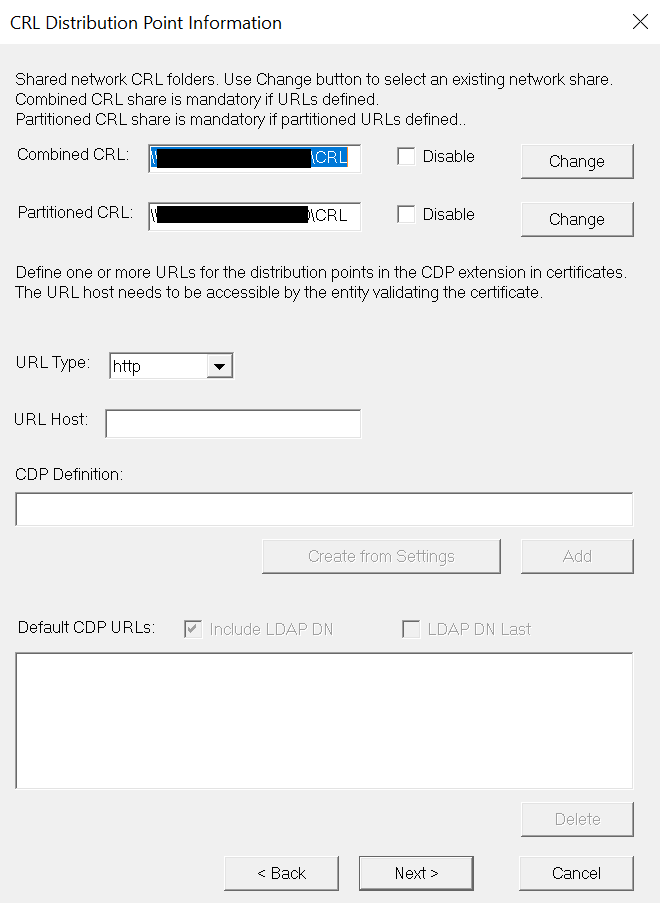
Step 3: OCSP / CRL Check
The browser also checks whether the certificate has been revoked using the Online Certificate Status Protocol (OCSP) or a Certificate Revocation List (CRL). An expired certificate may also show a revocation status change during this check.
Step 4: Warning Displayed
If any check fails, the browser refuses to establish a secure connection and displays a warning. The user sees an error — often with error codes like ERR_CERT_DATE_INVALID in Chrome or SEC_ERROR_EXPIRED_CERTIFICATE in Firefox.
Step 5: User Impact
At this point, the user either abandons the session (most users) or manually overrides the warning (a small minority of technically savvy users). Each abandoned session represents a real-world failure for Chase’s digital banking experience.
Suggested read: Online Marriage and Family Therapy Certificate Programs: Everything You Need to Know Before You Enroll
The Hidden Impact on Mobile Apps
Mobile applications handle certificate expiry differently. Chase’s iOS and Android apps use HTTPS for all communication, and many banks implement certificate pinning at the app level. When a pinned certificate expires and the app has not been updated to recognize the new certificate, the app may simply refuse to connect to the server — displaying a generic error message that gives no indication of the actual cause. This is one of the most frustrating aspects of Entrust R certificate expiry on Chase for mobile users.
Google’s Decision to Distrust Entrust Certificates
One of the most significant developments related to the Entrust R certificate expiration on Chase and other institutions is Google’s 2024 decision to distrust Entrust as a Certificate Authority in Chrome.
What Google Announced
In June 2024, Google’s Chrome Security Team announced that it would be removing Entrust’s root certificates from Chrome’s Root Store, effective November 1, 2024. This was a landmark and highly consequential decision.
“Google has lost confidence in the ability of Entrust to live up to the standards required of a Certificate Authority trusted by Chrome.” — Google Chrome Security Team, June 2024 ¹
Why Did Google Distrust Entrust?
Google cited a pattern of compliance failures by Entrust, including:
- Failure to revoke mis-issued certificates within required timelines
- Inaccurate responses to incidents raised by the security community
- Repeated compliance failures documented in the CA/Browser Forum discussions
- Lack of remediation despite multiple opportunities and communications
Practical Consequences for Chase Customers
The practical consequence was stark: any website using an Entrust-issued certificate would display an error in Chrome after November 1, 2024, unless the website migrated to a certificate from a different, still-trusted CA. For Chase customers, this meant that if Chase had any active Entrust certificates on its web properties and had not migrated by the deadline, Chrome users — who represent over 60% of the global browser market share — would see security warnings when visiting Chase’s websites. This is one of the primary reasons “certificate entrust r expires chase” became such a widely searched topic in late 2024.
How Banks Responded to Google’s Distrust Decision
Most major financial institutions that relied on Entrust certificates began emergency certificate replacement programs in mid-2024. This involved:
- Auditing all active Entrust certificates across all web properties
- Purchasing replacement certificates from alternative CAs such as DigiCert, Sectigo, or Let’s Encrypt
- Deploying new certificates without causing service interruptions
- Updating any mobile apps that used certificate pinning tied to Entrust roots
- Testing all deployment changes across browsers and operating systems before go-live
Source: ¹ Google Chrome Security Blog — Sustaining Digital Certificate Security
How to Check If the Entrust R Certificate Expired on Chase
If you are a Chase customer and you are experiencing issues accessing your account, here is how you can check whether the Entrust R certificate on Chase is the culprit.
Suggested read: What Is a Digital Certificate Manager and Why Does Your Business Need One?
Method 1: Browser Certificate Inspector (Desktop)
Google Chrome:
- Navigate to chase.com
- Click the padlock icon (or the info icon) in the address bar
- Click “Connection is secure” → “Certificate is valid”
- Review the “Valid to” date and the “Issued by” field
If the “Issued by” field shows Entrust and the “Valid to” date has passed (or is very close), you have identified the issue.
Mozilla Firefox:
- Navigate to chase.com
- Click the padlock icon → “Connection secure” → “More information”
- In the Page Info window, click “View Certificate”
- Review the Validity Period section
Method 2: Online SSL Checker Tools
Several free tools allow you to inspect a site’s certificate without needing to be in front of the browser:
| Tool | URL |
|---|---|
| SSL Labs Server Test | ssllabs.com/ssltest |
| DigiCert SSL Checker | digicert.com/help |
| GlobalSign SSL Check | globalsign.com/ssl-check |
| Why No Padlock | whynopadlock.com |
Simply enter chase.com into any of these tools to get a full certificate chain analysis, including expiration dates, issuing CA, and any detected problems.
Method 3: Command Line (Advanced Users)
For technically inclined users, the following OpenSSL command can check the certificate directly:
echo | openssl s_client -connect chase.com:443 -servername chase.com 2>/dev/null | openssl x509 -noout -dates -issuer
This outputs the issuer name, the “notBefore” date (when the certificate became valid), and the “notAfter” date (when it expires).
What Should Chase Customers Do When Certificates Expire?
If you are encountering a certificate warning when trying to access Chase’s online banking — and you believe it may be related to an Entrust R certificate expiration — here are the steps you should take.
Suggested read: What Is a Central Station Alarm Certificate and Why Does Every Homeowner Need One?
Immediate Actions for Everyday Chase Users
- Do not click through certificate warnings on banking websites. Unlike some informational websites where the risk may be lower, financial sites demand full certificate trust. Clicking “proceed anyway” on a banking site’s certificate warning could expose you to a man-in-the-middle attack.
- Try a different browser. Different browsers maintain slightly different root stores and update them on different schedules. If Chrome shows a warning but Firefox does not (or vice versa), this can help you determine whether the issue is browser-specific.
- Check Chase’s official status page. Chase maintains service status information that can confirm whether a widespread issue is occurring. You can also check DownDetector for real-time user reports.
- Use Chase’s mobile app as an alternative. If the web browser is showing certificate warnings, the mobile app may still be functional — especially if it uses a different certificate pinning configuration.
- Contact Chase support directly. If you suspect a certificate issue is preventing you from accessing your account, call Chase’s customer service line at 1-800-935-9935 or use the in-app messaging function.
Longer-Term Considerations for Business Customers
If you manage a business that integrates with Chase’s APIs or online banking portal, certificate expiration incidents underscore the importance of:
- Setting up automated certificate monitoring using tools like Datadog, Dynatrace, or Sectigo Certificate Manager
- Subscribing to Chase’s developer portal notifications for any API or infrastructure changes
- Maintaining a certificate inventory of all certificates your organization depends on — including third-party CAs like Entrust
- Implementing redundant authentication paths so that a single CA’s failure does not take down your entire integration
How Banks Like Chase Manage Certificate Renewal
Large financial institutions like Chase operate in a highly regulated environment where certificate lifecycle management is both a security imperative and a compliance requirement.
Certificate Lifecycle Management (CLM) Platforms
Modern banks use automated Certificate Lifecycle Management platforms to track thousands of certificates simultaneously. These platforms typically:
- Automatically discover certificates across all web properties and internal systems
- Send alerts when a certificate is within 90, 60, and 30 days of expiration
- Automate renewal using the ACME protocol (the same protocol used by Let’s Encrypt) or vendor-specific APIs
- Enforce policy around minimum key lengths, approved algorithms, and maximum validity periods
Popular CLM platforms used in financial services include:
| Platform | Key Features |
|---|---|
| Venafi Trust Protection Platform | Enterprise-grade CLM, policy enforcement |
| Sectigo Certificate Manager | Automated renewal, broad CA support |
| DigiCert CertCentral | Multi-CA management, discovery tools |
| HashiCorp Vault | Secrets and certificate management, API-driven |
| Keyfactor EJBCA | PKI-as-a-service, compliance reporting |
Regulatory Requirements Banks Must Follow
Banks in the United States are subject to oversight from multiple regulators, including:
- The Office of the Comptroller of the Currency (OCC)
- The Federal Financial Institutions Examination Council (FFIEC)
- The Consumer Financial Protection Bureau (CFPB)
- The SEC (for investment banking operations)
The FFIEC IT Examination Handbook specifically addresses the need for financial institutions to maintain secure, authenticated connections — and certificate management falls squarely within that scope. Failure to maintain valid certificates can result in regulatory findings during examinations, adding a compliance dimension on top of the security and operational ones.
Case Studies: Certificate Expiration Incidents in Banking
Real-world incidents involving SSL certificate expiration in financial services are more common than most people realize. These case studies illustrate why certificate entrust r expires chase is a topic that resonates with both security professionals and everyday users.
Case Study 1: LinkedIn’s Certificate Expiry (2023)
While not a bank, LinkedIn’s 2023 certificate expiry incident — which affected millions of users globally for several hours — demonstrated the scale of disruption a single missed renewal can cause. LinkedIn’s security team scrambled to deploy a replacement certificate, but the incident highlighted that even large, well-resourced technology teams can miss certificate renewals.
Suggested read: Sterigenics ISO Certificate: Everything You Need to Know About Their Quality Certifications
Key Lesson: Certificate expiry does not discriminate by organization size or sophistication.
Case Study 2: Microsoft Azure Certificate Expiry (2022)
In January 2022, Microsoft Azure experienced a significant outage partly attributed to a certificate expiry in their authentication infrastructure. The incident affected multiple Azure services for several hours and impacted thousands of enterprise customers worldwide.
“Certificate-related outages are among the most preventable yet frequently occurring disruptions in enterprise IT.” — Gartner Research, 2023
Key Lesson: Even cloud-native, highly automated environments suffer from certificate expiry incidents when automation fails or edge cases are not accounted for.
Case Study 3: U.S. Government Certificate Incidents (Recurring)
The U.S. federal government has repeatedly made headlines for certificate expiry incidents. During the 2018–2019 government shutdown, dozens of federal websites displayed certificate warnings because the teams responsible for renewal were furloughed. Sites like the Department of Justice’s main portal were affected.
Key Lesson: Certificate management requires continuous operational attention and cannot be fully “set and forget” — even with automation in place.
Case Study 4: Entrust’s Trust Removal Impact on Financial Sector (2024)
Following Google’s 2024 decision to distrust Entrust, numerous financial institutions that had relied on Entrust certificates were forced into emergency certificate replacements. Reports from cybersecurity monitoring firms indicated that over 26,000 websites with active Entrust certificates needed migration before the November 2024 deadline.
For banks specifically, this was particularly challenging because:
- Many certificates were embedded deep in API gateways and middleware systems
- Some legacy systems required vendor firmware updates before they could accept new certificate formats
- Certificate pinning in mobile apps required new app releases and App Store / Play Store approval timelines
Key Lesson: Dependence on a single CA creates single-point-of-failure risk. Diversifying across multiple trusted CAs is a best practice for large institutions.
Suggested read: Is Advanced Medical Certification Legit? What You Need to Know Before Enrolling
FAQs About Certificate Entrust R Expires Chase
What does “certificate entrust r expires chase” mean?
It refers to an SSL/TLS certificate issued by Entrust (a Certificate Authority) to JPMorgan Chase that has reached or is approaching its expiration date. When this certificate expires, browsers display security warnings and users may be unable to securely access Chase’s online banking services.
Is it safe to ignore a certificate warning on chase.com?
No. You should never click through a certificate warning on a banking website. While the warning may sometimes be caused by a benign technical issue (like a certificate expiry), it could also indicate a genuine man-in-the-middle attack where a malicious party is intercepting your connection. When in doubt, do not proceed and contact Chase directly.
Why would Chase use Entrust certificates?
Chase and other major financial institutions have historically used Entrust because of Entrust’s long-standing reputation, compliance with government standards (Entrust holds numerous government-grade certifications), and their ability to support high-assurance Extended Validation (EV) certificates that display the organization’s name in browser UI elements.
What did Google’s distrust of Entrust mean for Chase customers?
Starting November 1, 2024, Google Chrome stopped trusting new Entrust certificates. This meant any Chase web property still relying on an Entrust certificate issued after October 31, 2024 would display security warnings to Chrome users. Chase would have needed to migrate to certificates from a different trusted CA to avoid disrupting the majority of its online users.
How often do SSL certificates need to be renewed?
Since September 2020, the maximum validity period for publicly trusted SSL/TLS certificates has been 398 days (approximately 13 months). Before that, certificates could be valid for up to 2 years. The CA/Browser Forum continues to push for even shorter validity periods — proposals for 90-day maximums have been circulating and are likely to become standard in the coming years.
Can a certificate expiry lead to a data breach?
A certificate expiry itself does not directly cause a data breach. However, an expired certificate means that the encryption and authentication that protect your connection are no longer verifiable. This creates a window where an attacker could potentially intercept communications through a man-in-the-middle attack, especially if users click through security warnings.
What is the Entrust R3 certificate?
Entrust R3 is one of Entrust’s intermediate Certificate Authority certificates. It sits between Entrust’s root CA and the end-entity certificates issued to organizations. If the Entrust R3 intermediate certificate expires or becomes untrusted, all certificates that chain up through it will also become untrusted — even if the end-entity certificate itself is still within its validity period.
Where can I verify if Chase’s certificate is currently valid?
You can check Chase’s SSL certificate status using free tools like SSL Labs (ssllabs.com/ssltest), DigiCert’s SSL Checker, or simply by clicking the padlock icon in your browser’s address bar when visiting chase.com. These tools will show you the current certificate issuer, validity period, and any detected issues.
If I completed a drug treatment program, do I need a certificate for that?
If you are looking for information about a certificate of completion drug treatment program, that is a completely separate document from SSL certificates. A drug treatment completion certificate is a formal document issued by a licensed treatment provider confirming your successful completion of a rehabilitation or treatment program. It carries no relation to digital security certificates.
Take Action: Check Your Certificate Entrust R Status on Chase Today
Don’t wait for a browser warning to discover that your banking connection is at risk. Whether you are a Chase customer, a developer integrating with Chase’s APIs, or a security professional responsible for your organization’s PKI posture, staying informed about certificate entrust r expires chase issues is essential.
Here is what you can do right now:
- ✅ Visit SSL Labs and run a free test on chase.com to check the current certificate status
- ✅ Enable browser notifications or use a certificate monitoring tool to receive alerts before certificates expire
- ✅ If you are a Chase Business customer, review your API integration certificates and confirm they do not rely on expiring Entrust roots
- ✅ Contact Chase’s technical support at 1-800-935-9935 if you are experiencing access issues that may be certificate-related
- ✅ Share this article with your IT team or security colleagues — certificate awareness saves organizations from avoidable outages
Sources and References
¹ Google Chrome Security Blog – Sustaining Digital Certificate Security — Entrust Certificate Distrust
² Venafi – 2023 Machine Identity Management Development Fund Research
³ CA/Browser Forum – Baseline Requirements for SSL/TLS Certificates
⁴ FFIEC IT Examination Handbook – Information Security Booklet
⁵ IBM Security – Cost of a Data Breach Report 2024